

Aggregate logs, events, and telemetry from cloud, on-prem, hybrid, OT, and applications into a scalable, unified data lake.
Run instant searches and correlations across massive data volumes for faster threat detection.
Ingest structured, semi-structured, and unstructured data with automated normalization and enrichment.
Correlate signals from diverse tools to detect patterns, anomalies, and complex multi-stage attacks efficiently.
Break silos and gain a unified view of all security signals across assets and environments.
Correlated, enriched data speeds up analysis and reduces investigative effort.
Handle large enterprise data volumes without performance degradation.
Access organized, contextualized data that supports faster, smarter SOC response.
Optimize retention and storage tiers to keep budgets under control.
A flexible, extensible design that supports evolving tools, workloads, and regulations.
NewEvol’s Unified Data Architecture gives SOC teams a single, high-performance environment to manage and analyze security data. With dashboards, intelligent normalization, correlation graphs, and visual mapping, teams detect anomalies, uncover relationships, and understand attack paths efficiently across any environment.
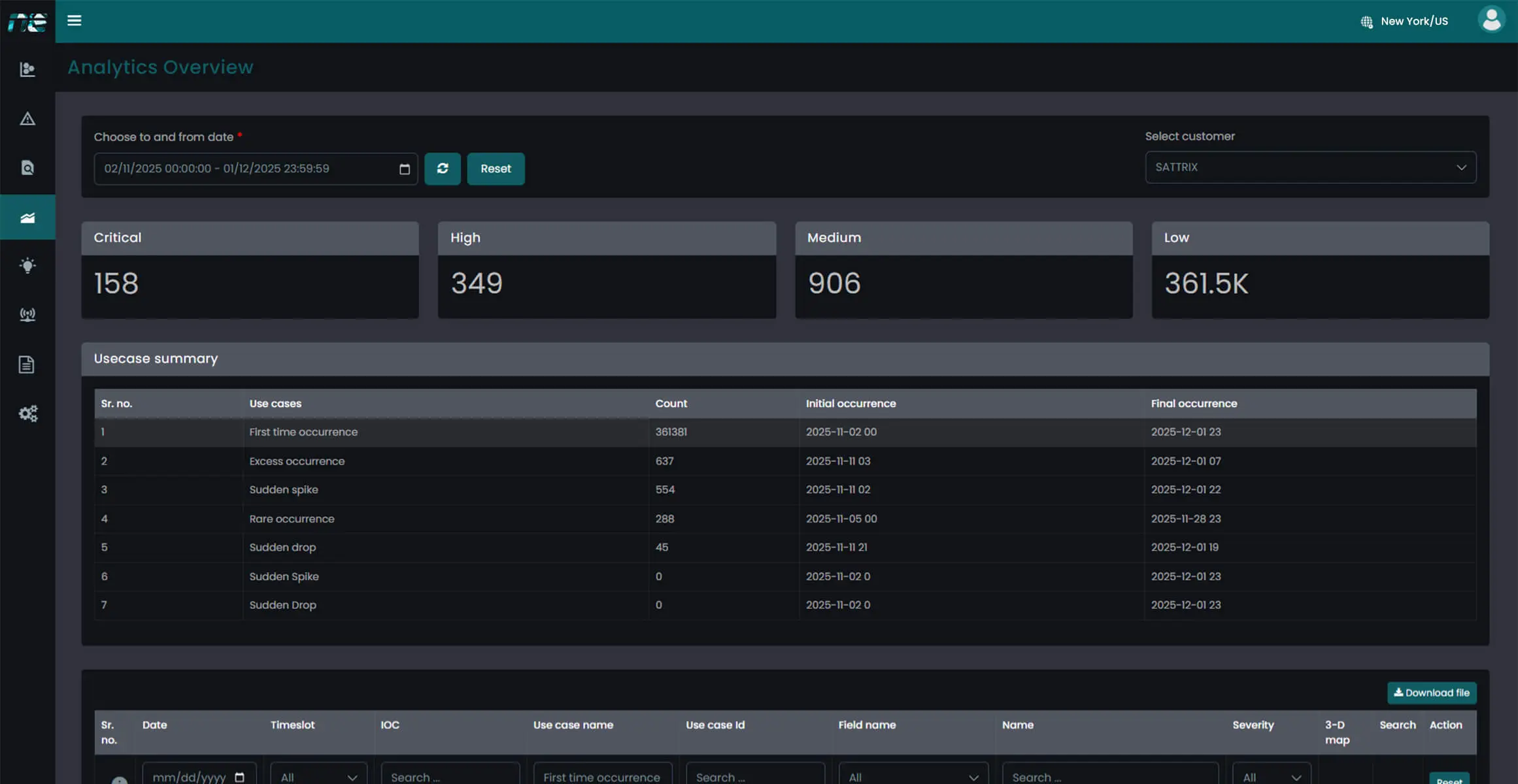
Collect and standardize logs, alerts, and telemetry from every security, cloud, and infrastructure source.
Use a scalable data lake with intelligent tiering to retain, classify, and optimize security data.
Detect patterns and anomalies with unified correlation models and high-speed querying.
Leverage dashboards, charts, mapping tools, and AI-driven insights to support rapid security decisions.
Build a scalable, intelligent, future-ready security data foundation with NewEvol, unifying fragmented visibility into seamless, actionable analytics across environments.
Talk to an Expert Our SolutionsRansomware attacks have become one of the most disruptive cybersecurity threats across the USA. These attacks can lock critical systems, encrypt sensitive data, and demand ransom payments within minutes of infection. For many organizations, manual response methods are too slow to...
Learn More
Protect your enterprise with smarter, faster security and gain real-time visibility across your entire IT environment.