

use cases
integrations
Continuously learn normal user and entity behavior to detect subtle anomalies, deviations, and suspicious activity.
Assess user risk levels based on login behavior, access patterns, privilege usage, and threat intelligence context.
Identify malicious actions, account takeover, credential misuse, and attempted data exfiltration in real time.
Track access, movement, file activity, cloud interactions, and system changes to uncover suspicious intent.
Identify unusual behavior before it becomes a security incident.
Spot account takeovers and unauthorized access immediately.
Correlated events and risk scoring minimize manual analysis.
Gain complete visibility into privilege usage and user actions.
Maintain traceable records of user behavior and access events.
Leverage intelligence fine-tuned for USA, MEA, India, Spain, and Malaysia.
The NewEvol UEBA Dashboard gives analysts unified visibility into user behavior across systems, applications, and cloud environments. It highlights risk scores, anomalies, and access deviations, while drill-down timelines and identity heatmaps help teams validate alerts, understand intent, and act quickly against internal threats.
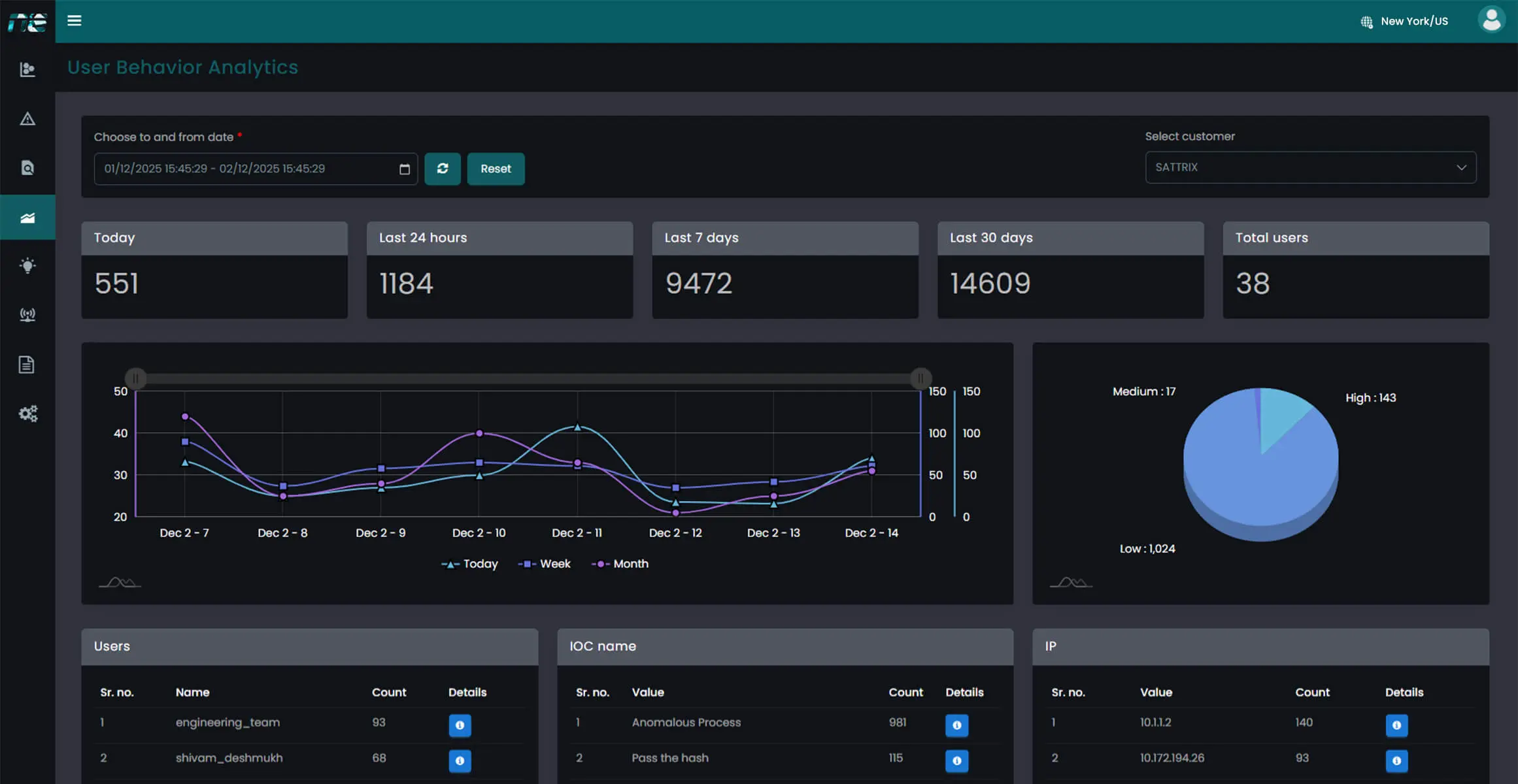
Ingest user activity, identity data, and entity logs to establish behavioral baselines.
Use machine learning to detect deviations, anomalies, and suspicious user patterns.
Assign risk scores using context, intelligence, and historical behavior models.
Trace behavior patterns, validate anomalies, and initiate automated or guided responses.
Strengthen internal security with AI-driven insights that detect compromised accounts, abnormal actions, and insider threats across global operations and worldwide digital environments.
Talk to an Expert Our SolutionsCybersecurity threats have become more frequent, complex, and costly for organizations of all sizes. Businesses face challenges such as ransomware attacks, phishing campaigns, insider threats, and data breaches that can disrupt operations and damage customer trust. As security en...
Learn More
Protect your enterprise with smarter, faster security and gain real-time visibility across your entire IT environment.