

Identify unknown threats using ML-based anomaly detection, pattern analysis, and predictive risk scoring.
Analyze user, system, and network behavior to uncover lateral movement, privilege misuse, and covert reconnaissance.
Combine global IOCs, TTPs, MITRE insights, and contextual intelligence to uncover sophisticated attacks.
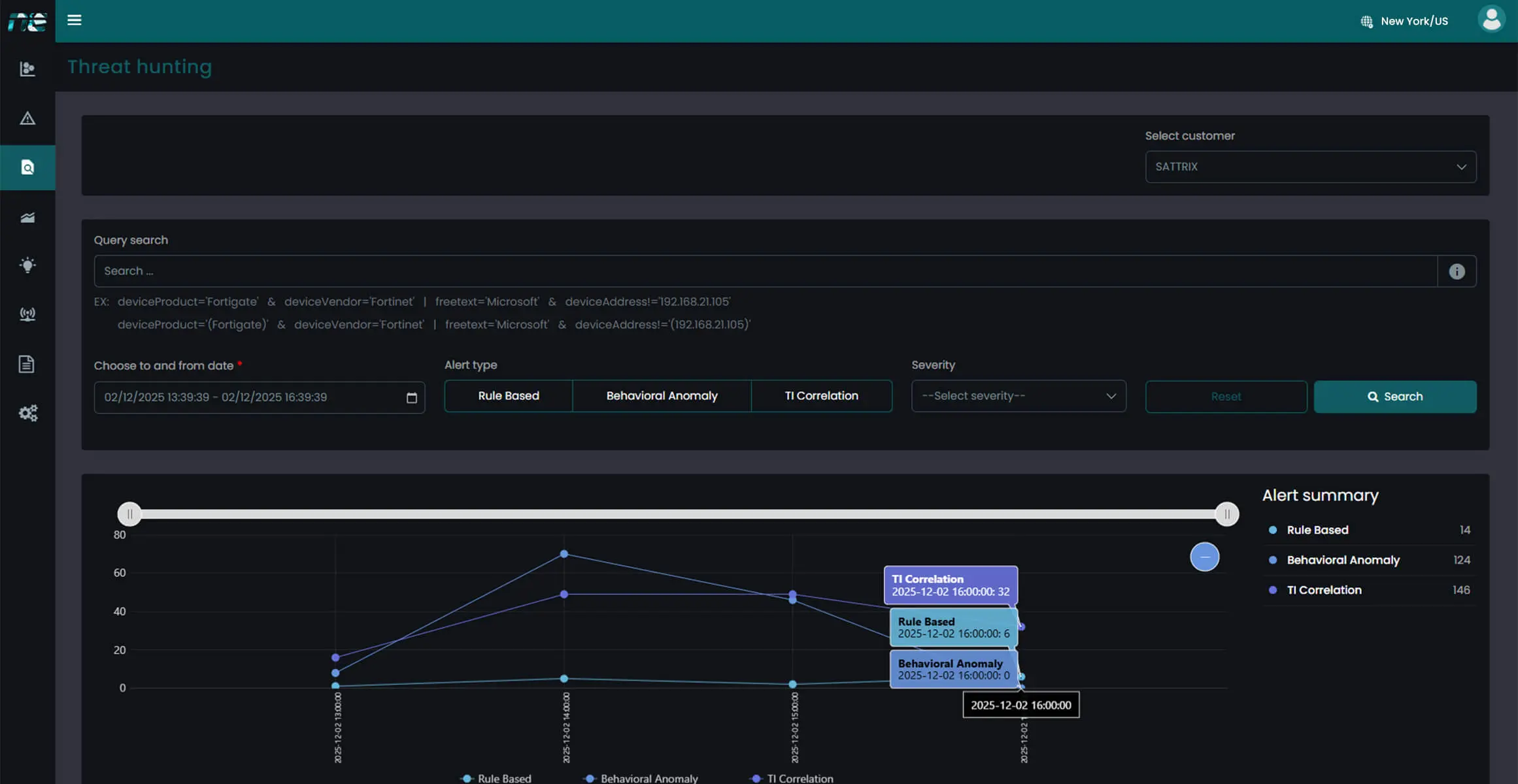
Automate hunt queries, execute guided investigation steps, and visualize threat trails across the enterprise.
Uncover stealthy, low-and-slow attacks missed by traditional tools.
AI-driven correlation ensures relevant, high-quality detections.
Pinpoint malicious behavior quickly to stop attackers early.
Pre-built hunt workflows save time and reduce manual effort.
Gain evidence-backed insights for audits, assessments, and governance.
Stay protected against threats active in USA, MEA, India, Spain, and Malaysia.
The NewEvol Threat Detection Dashboard brings anomalies, threat indicators, behavior deviations, and correlation graphs together in one unified interface. Analysts can trace potential attack paths, validate indicators, explore event timelines, and launch hunts instantly—turning complex threat data into clear, actionable intelligence.
Collect logs, telemetry, and user signals to build behavioral baselines.
Apply ML, threat intelligence, and event correlation to uncover anomalies and covert attack patterns.
Use contextual insights, threat trails, and guided workflows to explore suspicious behavior.
Automate responses, refine detection models, and evolve hunting strategies continuously.
Detect advanced threats with AI-driven analytics and global intelligence, helping organizations worldwide stay proactively secure across all digital environments.
Talk to an Expert Our SolutionsCyber threats are growing rapidly across the Middle East, Africa, and India. Enterprises of all sizes are facing ransomware attacks, phishing campaigns, insider threats, and data breaches that can disrupt operations and damage customer trust. As businesses continue to move worklo...
Learn More
Protect your enterprise with smarter, faster security and gain real-time visibility across your entire IT environment.