

Connect events across endpoints, networks, cloud, and applications to reveal attack paths and root causes.
Standardized workflows and automated steps help analysts contain, mitigate, and resolve incidents efficiently.
Enrich alerts with context—IP reputation, user behavior, file metadata, and threat intelligence—for faster decision-making.
Drill down into logs, timelines, user actions, and system behaviors to reconstruct incidents with clarity.
Automate data collection, correlation, and evidence analysis.
Reduce human error with structured playbooks and AI-assisted findings.
Contain threats early to prevent lateral movement and minimize business disruption.
Enable teams to handle more incidents with fewer manual steps.
Generate clear, traceable investigation records for compliance.
Benefit from region-specific intelligence across USA, MEA, India, Spain, and Malaysia.
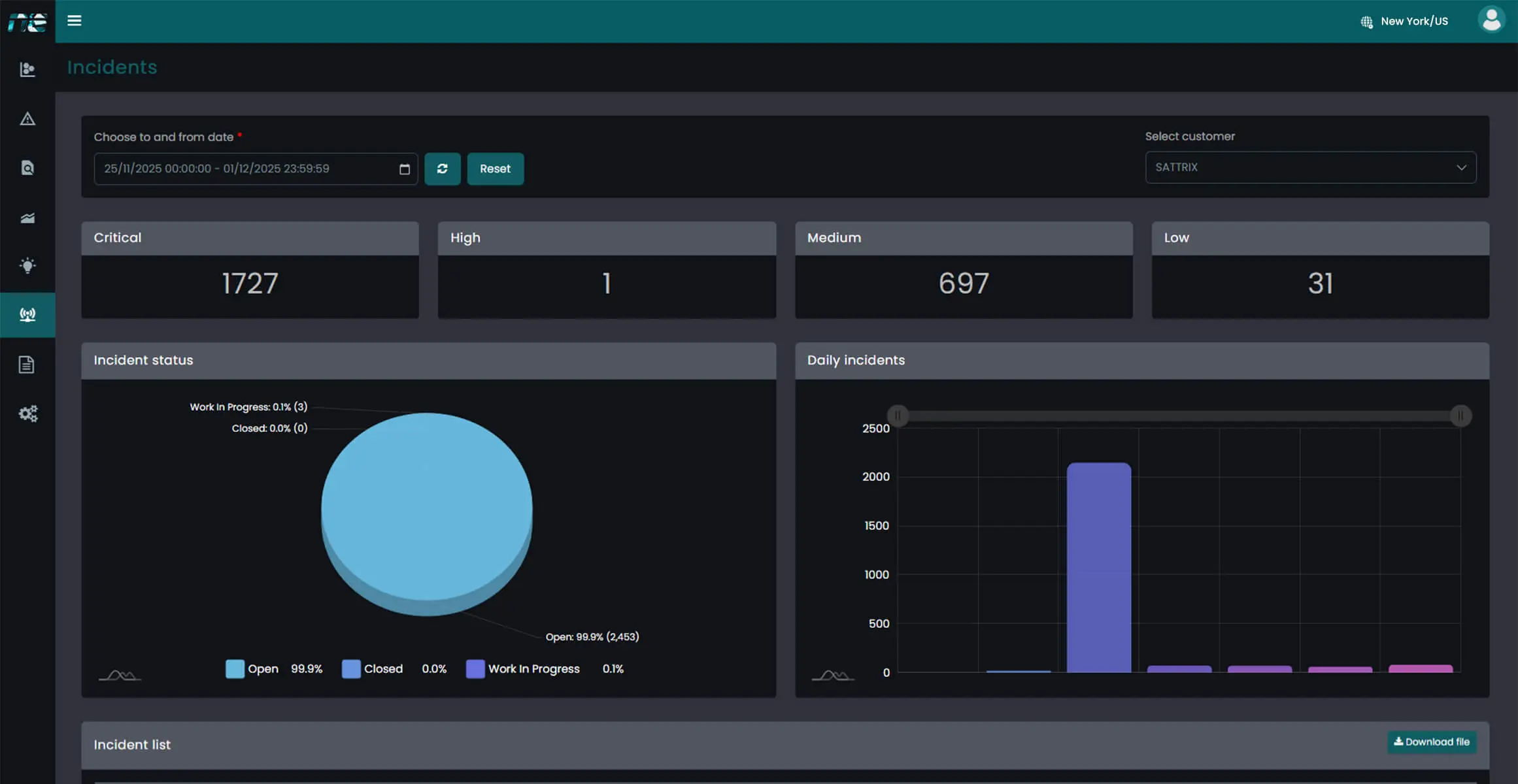
NewEvol’s Real-Time Monitoring Dashboard gives analysts a continuously updated view of threats, events, and suspicious activities across all environments. Interactive charts, heatmaps, correlation timelines, and drill-down filters enable teams to validate risks, trace attack origins, and act decisively—all from one intelligent interface.
Collect alerts and telemetry from SIEM, EDR, cloud, and network tools.
Use AI to link related events and enrich evidence with threat intelligence.
Determine scope, severity, impacted assets, and recommended actions.
Initiate guided response steps or automated workflows for rapid containment and remediation.
Accelerate investigations with AI, automation, and unified visibility, helping SOC teams across all regions detect, analyze, and respond efficiently.
Talk to an Expert Our SolutionsSecurity Operations Centers across the USA are under pressure like never before. Analysts deal with endless notifications, duplicate incidents, false positives, and manual tasks that consume valuable time. The result is burnout, slower response times, and missed threats hiding in...
Learn More
Protect your enterprise with smarter, faster security and gain real-time visibility across your entire IT environment.